Smart Building IoT Platforms: Data Security
Protecting Data at Every Layer of the IoT Platform

Protecting Data Integrity
Data integrity is paramount in today's interconnected world. Ensuring that data remains accurate, consistent, and reliable throughout its lifecycle is crucial for maintaining trust and preventing costly errors. This encompasses a wide range of processes, from initial data collection to final reporting, and requires a multi-faceted approach.
Robust data validation procedures are essential to identify and correct inconsistencies at the source. Thorough testing and quality control measures, implemented at each stage of the data processing pipeline, can significantly reduce the risk of errors propagating through the system.
Data Security in Cloud Environments
With the increasing reliance on cloud-based services, safeguarding data in these environments is critical. Employing strong access controls, encryption protocols, and regular security audits are vital to protect sensitive information from unauthorized access and breaches. Organizations must also carefully consider the security posture of their chosen cloud providers and ensure compliance with relevant industry regulations.
Data encryption is a cornerstone of cloud security, ensuring that data remains confidential even if compromised. Regular security assessments and penetration testing are also important to proactively identify vulnerabilities and mitigate potential risks.
Data Backup and Recovery Strategies
Data loss can have devastating consequences, impacting operations, reputation, and financial stability. Implementing a robust data backup and recovery strategy is thus essential. This includes regular backups of critical data, stored in secure off-site locations, to ensure recovery capability in case of disaster or data corruption.
Maintaining multiple backup copies, and testing their restoration capabilities, is vital for ensuring business continuity. Regularly reviewing and updating backup and recovery procedures is crucial to adapt to evolving threats and data storage needs.
Access Control and User Management
Implementing robust access control mechanisms is essential to protect sensitive data from unauthorized access. Granular permissions and role-based access controls (RBAC) ensure that users only have access to the data and functionalities necessary for their roles. This minimizes the potential for malicious activity or accidental data breaches.
Regularly reviewing and updating user access permissions is critical to maintain a secure environment and prevent unauthorized access. Strong password policies, multi-factor authentication, and regular user account reviews are also integral components of a comprehensive access control strategy.
Physical Security and Environmental Controls
Data centers and other physical locations housing sensitive data require robust physical security measures to prevent unauthorized access and environmental damage. This includes security personnel, surveillance systems, and access control systems that limit entry to authorized personnel. Maintaining a secure and controlled environment is crucial for preserving the confidentiality and integrity of the data stored.
Protecting data from natural disasters and other environmental hazards is also crucial. Redundant power and cooling systems, as well as disaster recovery plans, can minimize disruption and ensure business continuity during unforeseen events. Disaster preparedness is an important aspect of overall data protection.
The Importance of Data Encryption and Authentication
Data Encryption for Secure IoT Communication
Data encryption is crucial for safeguarding sensitive information transmitted between devices and the central building management system in a smart building IoT platform. Encryption transforms readable data into an unreadable format, preventing unauthorized access even if the data is intercepted. This is paramount in a smart building environment where various IoT devices collect and exchange crucial information, including environmental readings, security footage, and energy consumption data. Without robust encryption protocols, this sensitive information becomes vulnerable to breaches, potentially leading to significant financial losses and reputational damage.
Implementing strong encryption algorithms, like AES-256, is essential. These algorithms ensure that only authorized parties can decipher the encrypted data. Furthermore, establishing a secure key management system is vital to maintain the confidentiality and integrity of the encryption keys. This involves secure storage and regular updates of these keys to mitigate potential vulnerabilities.
Authentication for Verified Device Identity
Authentication mechanisms verify the identity of devices connecting to the smart building platform. This is critical to ensure that only legitimate devices are allowed to access the system and its resources. Without robust authentication, malicious actors could potentially introduce compromised or fraudulent devices, leading to data breaches or system disruptions. Strong authentication processes establish trust and prevent unauthorized access to valuable data and control systems.
Implementing multi-factor authentication (MFA) adds an extra layer of security. MFA requires multiple forms of verification, such as a password and a one-time code sent to a registered device, making it significantly harder for unauthorized users to gain access. Using device fingerprints and certificates further enhances the security and reliability of the authentication process.
Protecting Against Data Breaches
Data breaches are a significant threat to smart building IoT platforms. Protecting against unauthorized access and data exfiltration is paramount for maintaining the integrity and confidentiality of the collected information. A comprehensive security strategy must consider various attack vectors, including network vulnerabilities, malicious software, and social engineering tactics.
Implementing intrusion detection and prevention systems (IDS/IPS) helps identify and mitigate potential threats in real-time. Regular security audits and vulnerability assessments are essential to proactively identify and address potential weaknesses in the system. These measures, when combined with strong data encryption and authentication, significantly reduce the risk of data breaches.
Ensuring Data Integrity and Non-Repudiation
Data integrity ensures that the data remains unaltered during transmission and storage. Implementing mechanisms that verify the authenticity and integrity of the data is crucial in a smart building environment. This prevents tampering with data, which could lead to incorrect decisions based on faulty information. Using cryptographic hash functions is one way to ensure data integrity.
Non-repudiation ensures that the sender of the data cannot deny sending it. This feature is critical for maintaining trust and accountability within the system. Implementing digital signatures and timestamps can help establish non-repudiation, providing evidence of the origin and time of data transmission. This is especially important in situations where data accuracy and reliability are paramount.
Scalability and Adaptability of Security Measures
As smart building IoT platforms grow and evolve, security measures must be scalable and adaptable to accommodate new devices and functionalities. The security architecture should be designed with future needs in mind to ensure that it can handle increasing data volumes and evolving threats. This requires a flexible and robust system that can be easily updated and maintained.
Regular security updates and patches are essential to address any newly discovered vulnerabilities. Monitoring and analyzing security logs to identify and respond to suspicious activities is crucial to maintain a proactive security posture. The security infrastructure should be designed to accommodate future growth, ensuring that the platform remains secure and reliable as the building evolves.
The Role of Human Factors in Security
While technical security measures are paramount, the human element plays a significant role in maintaining the security of a smart building IoT platform. Training employees on security best practices, including password management and reporting suspicious activities, is essential. Establishing clear security policies and procedures, and ensuring that all stakeholders understand their responsibilities related to data security, is vital.
Regular security awareness training programs can educate employees about common threats and how to avoid them. Encouraging a culture of security within the organization, where employees feel empowered to report security concerns, is essential for maintaining the overall security posture of the smart building. Human oversight and participation are critical for a successful and secure implementation of the platform.
Read more about Smart Building IoT Platforms: Data Security
Hot Recommendations
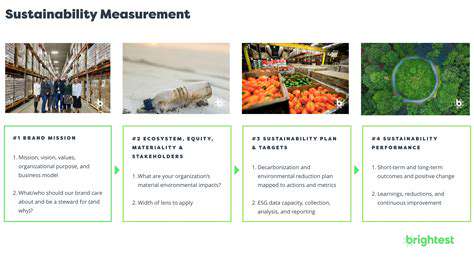
- Sustainable Real Estate Design Principles
- AI in Real Estate: Streamlining the Buying Process
- Climate Risk Disclosure: A Must for Real Estate
- Climate Risk Analytics: Essential for Real Estate Investment Funds
- Modular Sustainable Construction: Scalability and Speed
- Real Estate and Community Disaster Preparedness
- Smart Buildings and Advanced Building Analytics for Optimal Performance
- Smart Waste Sorting and Recycling in Buildings
- Sustainable Real Estate: A Strategic Advantage
- AI in Real Estate Transaction Processing: Speed and Accuracy